Incident Response
What is Incident Response? Process, Frameworks, and Tools
Incident response is the process of dealing with a data breach or cyberattack, including how an organization attempts to control the consequences of such an incident. The goal is to effectively manage incidents to minimize damage to systems and data, reduce recovery time and cost, and control damage to brand reputation.
Organizations must implement a clear incident response plan. This plan should state what constitutes a security incident and describe a straightforward process teams can follow when an incident occurs.
It is also important that organizations designate a team, employee, or leader responsible for managing the overall incident response initiative and executing on the plan. In a larger organization, this team is called the Computer Security Incident Response Team (CSIRT).
This is part of an extensive series of guides about network security.
Under attack? Get help from the BlueVoyant incident response team.
Why Is Incident Response Important?
Incident activity that is not properly controlled can escalate into a bigger problem, ultimately leading to data breaches, high costs, or system outages. By responding quickly to incidents, organizations can minimize losses, mitigate exploited vulnerabilities, restore services and processes, and mitigate the risk of future incidents.
Incident response enables organizations to do the following:
- Prepare for the known and the unknown
Immediately identify security incidents
Establish best practices to block intrusions before they cause damage
Incident response is critical to business, as most organizations’ operations rely on mission critical computing systems and store sensitive information. Security incidents can have short- and long-term impacts that affect the success of the entire organization. These can include downtime and service disruption, regulatory fines, legal fees, and data recovery costs.
Beyond these direct impacts, failure to effectively respond to incidents hurts the organization’s business performance. Unhandled incidents are associated with negative brand reputation and low levels of customer loyalty and satisfaction.
Although an organization cannot completely eliminate incidents, incident response can help minimize their occurrence. Organizations should focus on preparing for the impact of a security incident. Attackers will always be out there, but any organization can prepare for an attack with a functionally effective approach to incident response.
What Is an Incident Response Plan?
An incident response plan is a document that details the security processes to be carried out in case of an incident, and those responsible for incident response. An incident response plan typically includes the following details:
- Incident response methods and strategies
- How incident response can support your organization's broader mission
- Activities required for each stage of incident response
- Roles and responsibilities for completing incident response activities
- Communication channels between the incident response team and the rest of the organization
- Metrics for evaluating the efficiency of incident response
The benefits of an incident response plan don't end when a cybersecurity incident is resolved. The plan continues to provide support for litigation, documentation to submit to auditors, and historical knowledge that enables a better response to similar incidents in the future.
Learn how to build an incident response plan in our detailed guide
Incident Response Steps
A standard incident response plan that may be implemented by an organization includes the following steps:
Step 1: Early detection
A security event occurs, and the system detects it. Typically, the security information and event management (SIEM) platform alerts the incident response team.
Step 2: Analysis
Analysts review alerts, identify indicators of compromise (IoC), and use them to triage the threat. They will often perform additional testing, reviewing related alerts and ruling out false positives to get a complete picture of suspicious events.
Step 3: Prioritization
Analysts need to understand the impact of security incidents on the organization’s business activity and valuable assets. Prioritizing incidents helps a team understand which security events to focus on, and how to best manage resources in subsequent steps.
Step 4: Notification
First, the incident responder notifies the appropriate people within the organization. In case of a confirmed breach, organizations typically notify external parties, such as customers, business partners, regulators, law enforcement agencies, or the public. The decision to notify external parties is usually left to senior management.
Step 5: Containment and forensics
Incident responders take action to stop the incident and prevent the threat from reinfecting the environment. They also collect forensic evidence as needed for further investigation or future legal proceedings.
Step 6: Recovery
Incident responders eradicate malware from affected systems, then rebuild, restore from backup, and patch those systems to restore normal operation.
Step 7: Incident review
To prevent an incident from reoccurring and to improve future response, security personnel review the steps that led to the detection of the most recent incident. They identify aspects of successful incident response, opportunities to improve systems (such as tools, processes, and staff training), and recommend remediations for discovered vulnerabilities.
Learn more in our detailed guide to incident response steps
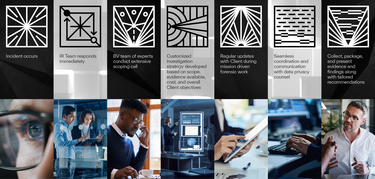
This is an example of BlueVoyant's incident response steps.
Incident Response Frameworks
Some large organizations with significant security expertise have developed incident response frameworks to help organizations create standardized response plans. The National Institute of Standards and Technology (NIST) and the SysAdmin, Auditing, Networking, and Security Institute (SANS) have each developed well-known incident response frameworks.
SANS Incident Response Framework
SANS is a private organization that works to investigate and educate the public on security issues. The SANS framework divides the incident response process into six phases:
- Preparation
- Identification
- Containment
- Eradication
- Recovery
- Lessons learned
SANS also includes an incident response checklist for each step and two templates with system commands to help organizations carry out specific incident response tasks. These templates are available for Windows and UNIX systems.
NIST Incident Response Framework
NIST is a US government agency that develops standards for the technology and security industry. As part of their cybersecurity work, they developed a comprehensive incident response framework. It includes details on creating an incident response plan, establishing an incident response team, building a communication plan, and training scenarios.
The framework condenses the six incident response steps used by the SANS framework into four:
- Preparation
- Detection and analysis
- Containment, eradication, and recovery
- Post-incident activity
NIST considers the containment, eradication, and recovery phases as overlapping. For example, while the system contains threats, an organization should not wait until all threats have been discovered before eradicating the problem. If other threats are present, they should be contained and eliminated as soon as possible. Also, recovery is not a strictly defined step but a process that depends on the prioritization and content of the assets being recovered.
Learn more in our detailed guide to incident response NIST
Incident Response Plan Templates
Developing an incident response plan can be difficult. Using one of the following templates provides structure and direction for this task:
- National Cyber Security Centre (NCSC) Planning guide—the NCSC is a key cybersecurity organization that provides cybersecurity assistance to major UK organizations.
- Sysnet’s Incident Response Template—this template outlines how to identify security incidents, the roles and responsibilities of key stakeholders and incident response planners, and the different types of incidents to consider.
- Incidentresponse.com—this site offers several playbooks for scenarios such as malware, phishing, and unauthorized access, all mapped to the NIST Incident Response Framework. These manuals are stand-alone documents separate from an incident response plan but should be referenced during its creation (learn more about incident response playbooks in the following section).
Learn more in our detailed guide to incident response plan template
Incident Response Playbooks
An incident response playbook provides teams with standard steps and procedures for responding to and resolving incidents in real time. Playbooks can also include peacetime training and exercises to prepare the team for the next event.
Playbooks are an integral part of DevOps and IT Ops incident management and cybersecurity. They help teams handle unplanned outages and restore systems to order, and their organizational policies and practices ensure a consistent response to incidents and security threats.
A playbook typically contains the following elements:
Runbooks
Checklists
Templates
Training exercises
Security attack scenarios
Simulation drills
Incident Response Team
Incident response teams are groups of IT professionals who prepare for and respond to cyber attacks. An incident response team's responsibilities include developing a proactive incident response plan, testing and resolving system vulnerabilities, maintaining strong security best practices, and providing support for all incident handling actions.
Incident response team members typically have varied skills, backgrounds, and roles, so they can prepare for a range of security incidents.
The specific skill set of organizations’ incident response teams may differ because companies have different personal risk profiles and business processes. In general, the core functions of incident response team members are:
- Leadership—coordinate the overall direction and strategy of response activities, freeing the rest of the team to focus on minimizing damage, recovering quickly, and operating efficiently.
- Investigation—coordinate efforts to determine the root cause of an incident, which helps to eradicate current threats and prevent future ones. To do so, it is important to gather as much relevant information as possible.
- Communications—manage relevant internal and external communications required for incident response. Communication may be required between teams and departments within an organization or with external stakeholders.
- Documentation—record incident response actions and activities.
- Legal representation—protect the organization by ensuring that incident response activities comply with laws and regulations.
A Framework for Leveraging Incident Response Tools
In addition to seeking administrative support and following a documented incident response plan, incident response tools are key to preparing for and responding to security incidents. Cybersecurity tools should be implemented long before an incident occurs, because they can provide critical information that can be used to detect, investigate, and respond to incidents.
Most organizations already have common security controls in place to support incident response capabilities, particularly with regard to logging and alerting. However, there are dedicated tools that can guide a team through its incident response workflow and provide all the details needed to make an informed decision.
Some organizations follow the Observe, Orient, Decide, Act (OODA) cycle to provide guidance on which tools are needed and when. This military approach to incident response follows a four-step approach to threats:
- Assess visibility of network traffic, operating system, and applications - establish a baseline for the organization’s environment and provides real-time information about what happened before, during, and after a security incident.
- Collect contextual information - gather detailed contextual information and intelligence about existing threats and running attacks.
- Collect real-time and forensic information - gather information about active, currently occurring threats and anomalous behaviors (as well as performing reactive, post-event research) to help security teams make informed decisions about how to respond.
- Address the threat - take steps to resolve the threat, minimize risk and business impact, and return to normal operations.
The OODA cycle can guide the use of incident response tools throughout the incident response process.
Incident Response Tool Categories
There are several types of tools that are useful for incident response:
Security Orchestration, Automation, and Response (SOAR)
SOAR refers to platforms that offer tools for collecting security data from various sources. A SOAR solution may combine machine learning and human input to analyze the data to extract insights and prioritize the relevant incident response procedures.
SOAR software typically includes three capabilities:
- Threat and vulnerability management
- Incident response
- Security operations automation
Organizations use SOAR to collect and make sense of threat-related data from diverse sources, enabling automated threat responses.
User and Entity Behavior Analytics (UEBA)
UEBA solutions use large datasets and machine learning to establish baselines for typical behavioral patterns, allowing them to identify atypical behavior within the network, which may indicate threats. The emphasis on suspicious behavior allows UEBA to detect threats that can evade traditional security and antivirus tools, including non-malware-based attacks.
UEBA uses behavioral models to assess threat levels, providing risk scores to guide the response process.
Security Information and Event Management (SIEM)
SIEM is a security management approach that provides a unified system to combine information and event management functions. SIEM solutions deploy multiple data collection agents to hierarchically collect event data from servers, end-user devices, and network infrastructure. A central management console consolidates the data, allowing security analysts to filter the noise and prioritize real security incidents.
Endpoint Detection and Response (EDR)
EDR systems collect and analyze endpoint security data to protect the network from vulnerable user devices and workstations. EDR aims to detect security breaches in real time, enabling rapid response. This approach helps identify emerging and advanced threats that traditional security tools might not. The specific capabilities of each EDR solution may vary significantly.
Extended Detection and Response (XDR)
XDR solutions are SaaS tools for detecting security threats and implementing incident response procedures. XDR tools integrate several security capabilities in a unified security operations solution, making sophisticated incident response capabilities more accessible and affordable.
The advantage of XDR is its consolidation of multiple security products building on EDR capabilities. It can improve the productivity of security operations with enhanced detection and response and centralized visibility and control across enterprise environments. XDR tools ingest and distill multiple telemetry streams and analyze threat vectors and tactics. They help speed up response efforts by handling the detection and investigation processes.
Learn more in our detailed guide to incident response tools
Incident Response Services
Incident response is most effective when undertaken quickly by experienced responders. Organizations often lack the resources to maintain a full incident response team that is active 24 hours a day. One option is to work with an external organization that provides professional incident response services.
Engaging with these organizations provides the following benefits:
- Availability—the sooner the incident response team gets to work, the lower the cost and the lower the impact of an attack on the organization. Cybersecurity incidents can occur at any time, and it can be difficult to reach incident response team members outside of business hours. Professional incident response providers have multiple teams of staff to provide better coverage and higher availability.
- Experience—mishandling security incidents can increase costs and damage an organization. For example, a ransomware attack can destabilize an infected system, which means that encrypted data may not be recovered upon reboot. Professional incident responders have the experience needed to handle such security incidents efficiently and accurately.
- Specialized expertise—incident response often requires expertise in areas such as forensic analysis and malware reverse engineering. While most companies won't need to have these skills in-house, a dedicated incident response team has access to the experts they need to handle cybersecurity incidents properly.
- Managing the entire incident response process—outsourced incident response providers should support all of the organization's incident response needs. This includes preparing for incident response, managing detected intrusions, and mitigating future attacks.
See Additional Guides on Key Network Security Topics
Together with our content partners, we have authored in-depth guides on several other topics that can also be useful as you explore the world of network security.
Microsegmentation
Authored by Tigera
- What is Microsegmentation? The Basics and Key Best Practices
- Application Segmentation: The Engine Behind Zero Trust
- Microsegmentation Security: The Evolution of Cybersecurity
SIEM
Authored by Exabeam
- What Is SIEM? Uses, Components, and Capabilities
- SIEM Log Management: The Complete Guide
- Security Big Data Analytics: Past, Present and Future
Security Operations Center
Authored by BlueVoyant
Solutions
Digital Forensics and Incident Response
BlueVoyant contains, remediates, investigates, and provides litigation support for your cyber crisis. We identify the breach’s root cause while simultaneously eliminating unauthorized access and minimizing business interruption.

Additional Readings

Incident Response
Incident Response Plan: Steps and 8 Critical Considerations

Incident Response
NIST Incident Response: Framework and Key Recommendations

Incident Response
Top 8 Incident Response Plan Templates
