Industry Insights
Update: Mobile Malware in the Finance Sector
February 6, 2020 | 2 min read
BlueVoyant

“Life in the SOC” is a Blog Series that shares experiences of the BlueVoyant SOC defending against the current and prevalent attacks encountered by our clients. The blogs discuss successful detection, response and mitigation actions that can improve your defensive capabilities.
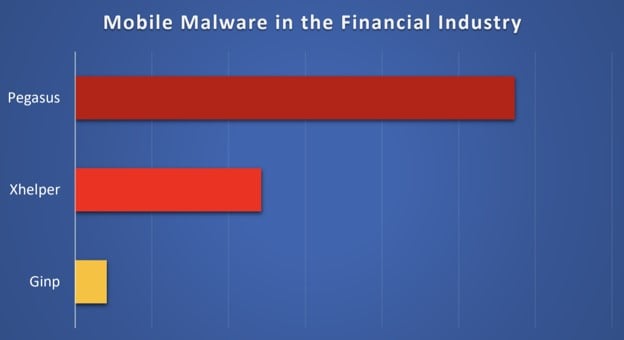
Mobile malware continues to be a constant threat to the financial sector. As previously reported, mobile malware is becoming an increasingly complex problem. In the month of November BlueVoyant observed three major players with ongoing campaigns.
Pegasus
Pegasus was developed by The NSO Group, an Israeli cyber-offense firm. The spyware was purportedly sold to government agencies for surveillance purposes. According to Citizen Labs, in order to monitor a target, a Pegasus government operator must convince the target to click on a specially crafted exploit link. If the target clicks on the link, a chain of zero-day exploits are delivered to penetrate security features on the phone and install Pegasus without the user’s knowledge or permission. Once the phone is exploited and Pegasus is installed, it begins contacting the operator’s C2 servers to receive and execute the operators’ commands, and send back the target’s private data.
Xhelper
Xhelper came on the scene in 2016. It recently made headlines for a number of reasons. In October of 2019, Symantec reported that the Android-based malware has infected over 45k devices in 6 months. There are reports that this malware can survive a factory reset and automatically reinstall itself if removed manually. Payloads are supplied by encrypted links from C2 servers.
There is much speculation about Xhelper, from who and where it targets, to what the purpose is. At this time, there is no attribution and it doesn’t seem to deliver an extremely malicious payload. It mostly shows advertisements. Researchers believe this may be part of a larger, more malicious attack. Payloads could change at any time based on what the C2 delivers. According to Symantec, Xhelper can’t be launched manually because there is no app icon visible on the launcher. Instead, the malicious app is launched by external events, such as when the compromised device is connected to or disconnected from a power supply, the device is rebooted, or an app is installed or uninstalled.
Ginp
Ginp is an Android trojan that has undergone multiple changes in a short time. The malware was first spotted in June 2019 posing as a “Google Play Verificator” app. Its objective is stealing SMS data by delivering the victim’s incoming and outgoing messages to a C2 server. It has since changed tactics.
In August 2019, researchers noted the malware on the Google Play Store disguised itself as an Adobe Flash Player update. Researchers from Threat Fabric determined that Ginp now steals login credentials and credit card information. It is currently targeting users in Spain and the U.K.
Threat Fabric recently released a report claiming that what makes this malware stand out is that it’s built from scratch, cherry-picking features from other malware families, such as Anubis. Researchers have spotted five new versions of this malware in as many months. In November, a new version was detected that has modifications that do not yet appear to be in use. It is believed that this malware will continue to expand in both functionality and target base.
Related Reading
Industry Insights
Ransomware in First Half of 2025: An Ecosystem in Flux
Managed Detection and Response
Why Microsoft Sentinel data lake Signals the Future of Security Operations