Industry Insights
Malware Targeting the Financial Sector - Part 2
January 30, 2020 | 2 min read
BlueVoyant

“Life in the SOC” is a Blog Series that shares experiences of the BlueVoyant SOC defending against the current and prevalent attacks encountered by our clients. The blogs discuss successful detection, response and mitigation actions that can improve your defensive capabilities.
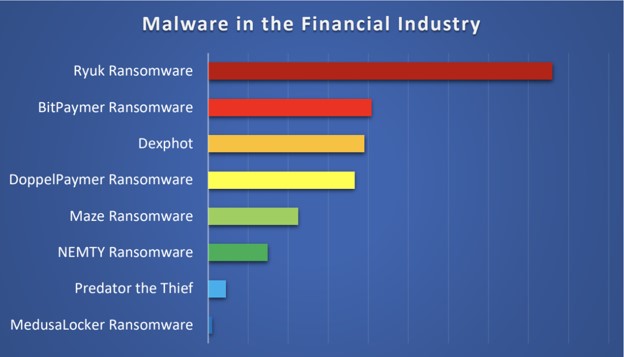
BlueVoyant’s December 2019 research identified malware targeting the financial sector. In Part 1 of this blog, we talked about Ryuk, BitPaymer, Dexphot and DopplePaymer. In Part 2 we will discuss Maze, Nemty, Predator the Thief and MedusaLocker ransomware.
Maze Ransomware
Maze ransomware is not brand new but has been increasingly active since May 2019. Operated by TA2101. Maze uses a number of delivery methods including exploit kits such as FallOut and Spelevo.
Maze made recent headlines after a breach of Allied Universal, a Californian-based security services firm. The attackers gave a deadline for ransom payment and threatened to leak victim data of the services firm. When Allied Universal refused to pay the ransom, the attackers leaked approximately 700 MB of data to WikiLeaks, BleepingComputer Forums, and Russian underground forums. The Maze crew states that this is only a small portion of the 5GB of data stolen in the process.
Nemty Ransomware
Nemty ransomware came on the scene in August 2019. While it first appeared to be a run-of-the-mill ransomware, a constant series of changes to the threat made it apparent that it was very much a work in progress and something to be taken seriously.
In the past, Nemty was spread via RIG exploit kit, as well as malicious spam campaigns targeting users in Korea and China, where the malware is attached inside an archive. In November, reports began surfacing indicating that this newer ransomware family has also partnered with TrickBot to increase its reach. Researchers from Symantec observed a recent version of TrickBot delivering a tiny component that uses the Server Message Block (SMB) protocol and a list of hardcoded credentials to try to connect to remote computers with port 139 open.
Predator the Thief
Predator is a data stealer developed by Russian-speaking individuals. It’s being sold cheaply on Russian forums and has been detected many times in the wild. Although detection is successful with previous versions, its owners are rapidly adapting it by generating FUD (Fully UnDetectable) samples every few days.
The owners selling the builder on underground markets. For a small additional payment they can also generate an administration panel for their affiliate attackers. The owners of Predator are very business oriented. They’re constantly updating their software, attempting to extend features, and adjusting to client requirements.
MedusaLocker Ransomware
MedusaLocker first came to light in September 2019. It has been observed in campaigns globally. This particular ransomware family has a few unique features designed to ensure it encrypts as much data as possible, not only on the locally infected machine but across a network. MedusaLocker’s ability to force connectivity to remote (mapped) drives combined with its persistence mechanisms are particularly problematic. The ransomware is commonly distributed through malspam campaigns. In analyzed samples, the malware has been attached directly in the email message.
Related Reading
Industry Insights
Ransomware in First Half of 2025: An Ecosystem in Flux
Managed Detection and Response
Why Microsoft Sentinel data lake Signals the Future of Security Operations