Supply Chain Defense
Malware and Campaigns of Interest
June 11, 2020 | 3 min read
BlueVoyant

“Life in the SOC” is a Blog Series that shares experiences of the BlueVoyant SOC defending against the current and prevalent attacks encountered by our clients. The blogs discuss successful detection, response and mitigation actions that can improve your defensive capabilities.
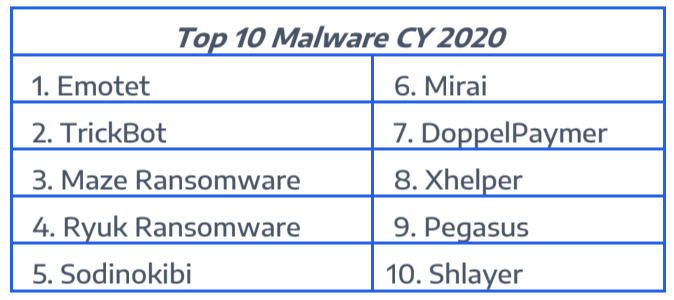
BlueVoyant performed analysis on the mentions of thousands of malware families across various internet forums to identify trends in the cybersecurity community. The following list represents the “Top 10” tracked malware strains for 2020 by most unique mentions totaled across the following forum categories: Mainstream News, Social Media and the Cyber Industry.
Notable malware and campaigns with increased mention across cyber forums include:
Xhelper
The Xhelper malware is a widely circulating Android backdoor that is able to survive factory reset. The malware was initially detected in May 2019 and has been frustrating victims ever since. In February, Malwarebytes researchers walked a tech-savvy user through troubleshooting and dislodging the backdoor; Malwarebytes did not determine how it maintained such persistence.
In April, Kaspersky Labs filled in the gaps, identifying how the Xhhelper persistence turned out to be the handiwork of a second-stage trojan known as Triada. Triada roots the Android devices and subsequently employs powerful system rights to write malicious files directly into the system partition while giving them an immutable attribute in the process. This enabled Xhelper to avoid deletion, even by superusers, and maintain persistence.
Dark Nexus
Dark Nexus is a new IoT Botnet profiled by Bitdefender researchers and assessed to have been constructed by a seasoned botnet author using Mirai and Qbot foundations. Dark Nexus has gained quick notoriety from its ability to vary its method of propagation through binaries cross-compiled for 12 different CPU architectures. It is also highlighted for its persistence and the way it disguises traffic as innocuous browser-generated traffic.
Agent Tesla
Agent Tesla is an information stealer that has been used in multiple recent phishing campaigns employing COVID-19 themes. In early April, Fortiguard Labs reported on a new variant of the trojan discovered in one such phishing campaign. The new variant syphoned data from web browsers, email and messenger clients, as well as VPN, FTP clients and download managers.
In a joint advisory issued mid-month by the UK National Cyber Security Centre and US Cybersecurity and Infrastructure Security Agency, Agent Tesla was one of three malware strains (with Netwire and LokiBot) being pushed in approximately 65 percent of COVID-19-associated phishing campaigns. Details of the new variant reported by Fortiguard Labs and this widespread usage indicate threat actors continue to adapt this trojan in various ways in order to optimize its utility and wreak more havoc.
Grandoreiro
Grandoreiro is a remote-overlay banking Trojan mostly observed targeting potential victims in Brazil and South America. Like many others, the remote-overlay malware is mostly spread via malspam campaigns, phishing pages or malicious attachments that users enable or load. Once it is installed, the malware bides its time and then launches into action when users access a hardcoded list of entities, mostly local banks. When a user enters a targeted website, the attacker is notified and then takes over the device remotely.
As the victim accesses their online banking account, the attacker can display a full-screen overlay image designed to appear like the user’s bank website. The overlaid pages can block the victim’s access to the site and allow the attacker to transfer funds after initial authentication or prompt the user to fill out additional data fields so as to glean further personal information on the victim.
In April IBM X-Force researchers observed and reported Grandoreiro migrating to Spain. The researchers conclude the attackers are either in cahoots with bad actors from Spain or have simply moved beyond their own continent. The recent campaign used COVID-19-themed videos to get users to click on a URL leading to a booby-trapped site.
Related Reading
Managed Detection and Response
Enhancing the Skills and Threat Detections of In-House SOCs and Security Teams
Supply Chain Defense
Navigating Cyber Threats in the Retail Sector